Description
This threat model is the deliverable of one of the finalists of our Spring 2023 Hackathon.
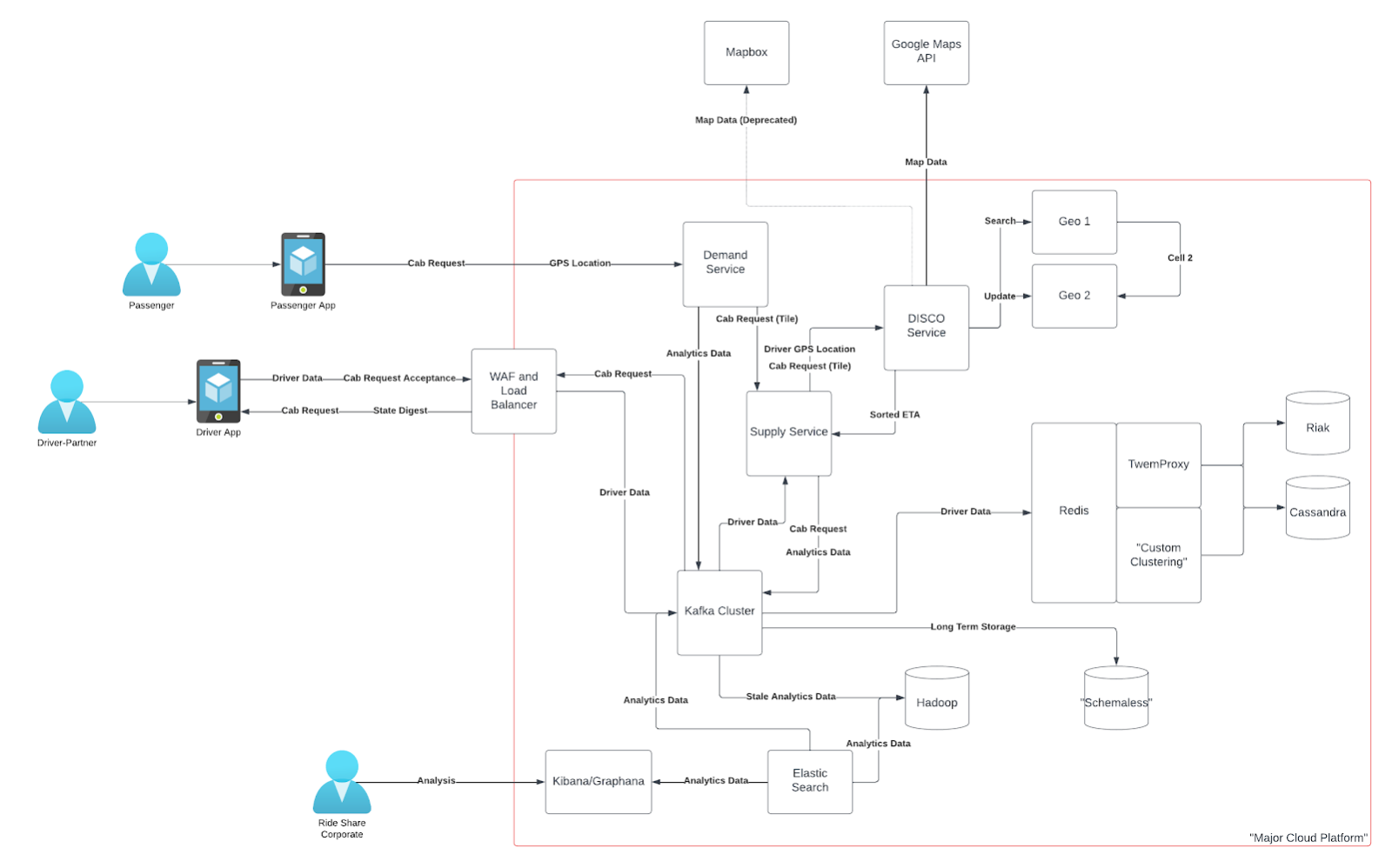
The team is tasked with threat modeling a rideshare app based on this use case. They used a combination of STRIDE and LINDDUN GO as their primary methodologies.
Creators
- Andrew Morehouse (
@morehouse_hacks ), Security and Compliance Analyst, Decisions, VA, US - Chris Ramirez (
@cramirez ), Principle Software Security Engineer, Axway, AZ, US - Duncan Hopewell (
@n1ffl3r ), Application Security Engineer, Kubota North America, TX, US - Nandita Rao Narla (
@Nandita ), Head of Technical Privacy and Governance, DoorDash, CA, US
Summary
Which threat modeling framework(s) used and why
We utilized STRIDE and LINDDUN GO, mostly because those were the models that the team had familiarity with.
Diagramming or thinking tool(s) used and why
LucidChart, because it was web based and allowed live collaboration.
What is the scope of the threat model?
What are the top 3 threats you identified? What are the mitigation plans?
- Abuse of the machine learning-driven access and pickup points. In order to mitigate, allow for user overrides of points and use that as feedback to detect poor.
- The collection of personal documents leads to significant personal information exposure. In order to mitigate, minimize the amount of time that personal documents are stored, and minimize the linkability of these documents or other personal information. In particular, limit the linkability within the analytics system.
- Denial of service against the demand service. The demand service uses web sockets, a resource-intensive technology, to have bi-directional communications. There isn’t any indication of a protective technology there that would prevent spamming. Mitigation is simply adding protective technology to the data flow.
How did you prioritize the threats for mitigation?
After enumerating threats, each threat was given a likelihood and impact rating to determine inherent risk. Additionally, each threat was rated for a level of effort for mitigating those threats. We then looked for the most risk reduction with the least effort.
How did you evaluate your threat model?
After completing the threat model, we looked at our overall process, identified where we struggled, and figured out how to characterize that in the retrospective section of our threat model.
Threat model
https://drive.google.com/file/d/1lffq0bSYeSmyTaW9Zh5ZArA3Q_nk445D/view?usp=sharing
Retrospective
If you were to give this threat model to the developer team, what do you think their reaction would be? How valuable do you think they’d find it?
The hope is always that the developer team will find it enlightening and useful. In this case, there were some limitations in the documentation provided that could have been solved with more developer interaction. The real value would have been found in building those relationships with the developers during the process and bringing their understanding into the final deliverable. They will likely be surprised, but hopefully, we have worded our threat model in such a way that it isn’t seen as an attack on their system.
What did you learn from this hackathon that will make you change/upgrade/refine the way you do threat modeling today?
Several of us on the team didn’t know that LINDDUN/LINDDUN GO existed. That really gave an artful way for us to include privacy concerns during the threat modeling process.
About the creators
The creators of this threat model is a team of one of the finalists of our Spring 2023 Hackathon. Let’s hear about their hackathon story.
Who are on your team?
-
Andrew Morehouse, Security and Compliance Analyst, Decisions, @VA, US
-
Chris Ramirez, Principle Software Security Engineer, Axway, @AZ, US
-
Duncan Hopewell, Application Security Engineer, Kubota North America, @TX, US (Captain)
-
Nandita Rao Narla, Head of Technical Privacy and Governance, DoorDash, @CA, US



How did you work together?
Because we are all busy professionals, in different time zones, with different familial demands, we needed to figure out a way to work asynchronously with each other. We were able to accomplish that via discussions in Slack, tracking progress in Trello, and accumulating results in Google Docs and Sheets.
What was the biggest challenge you faced? How did you overcome it?
“I believe the biggest challenge was making communication work despite differences in time zones. We overcame it by utilizing Slack and Google Drive to communicate with one another. For me, an aha moment was after looking at a diagram that Duncan had put together and realizing where I could begin the enumeration of vulnerabilities.” - Andrew Morehouse
About Threat Model Collections
In this content series, we’ll publish and curate different threat model examples. The threat models can take many forms, such as graphical, textual representations or code. The models use diverse technologies, methodologies and techniques.

