The threat model
This threat model is the deliverable of the champion of our Spring 2023 Hackathon.
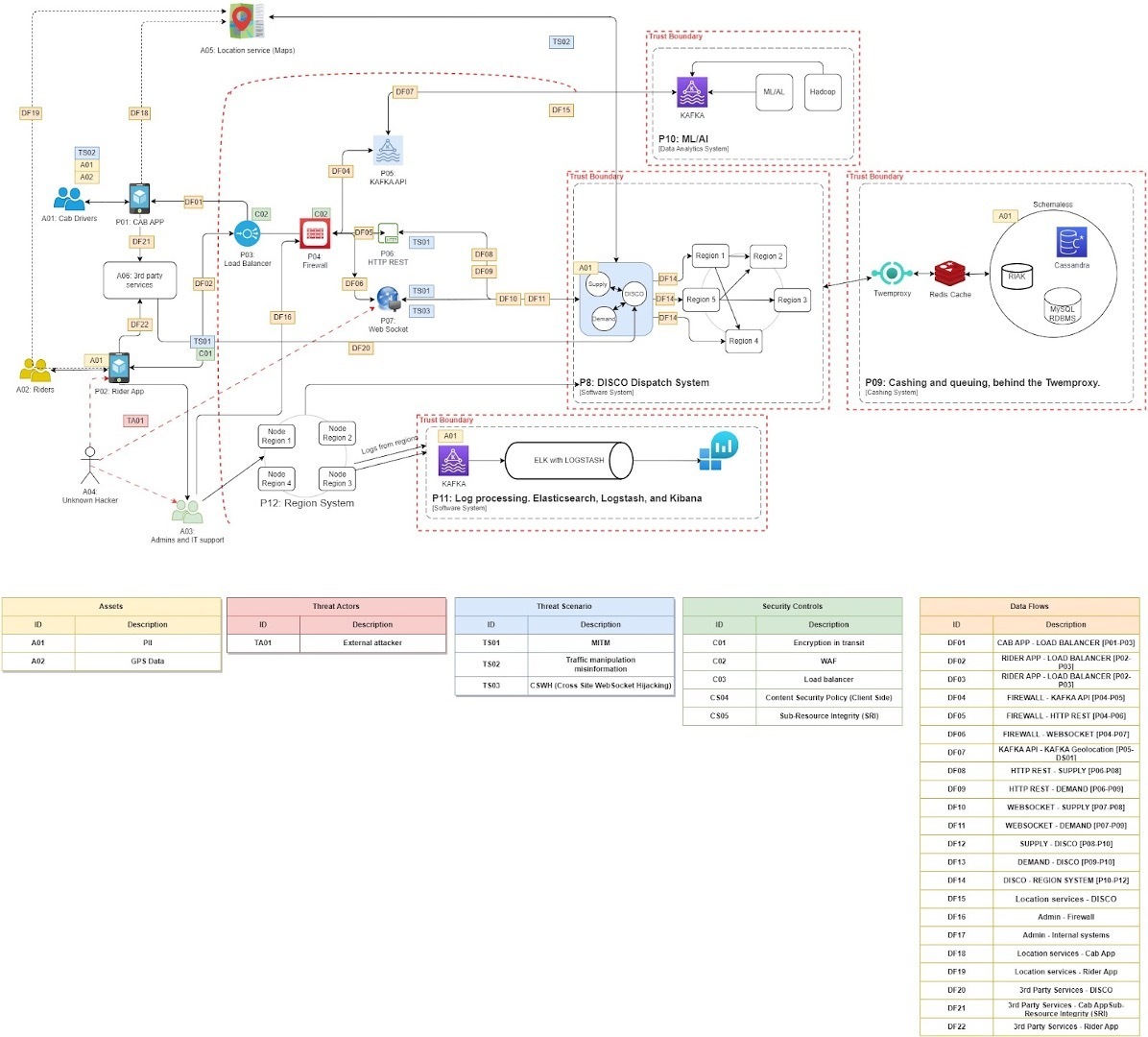
The team is tasked with threat modeling a rideshare app based on this use case. They used a combination of STRIDE and LINDDUN as their primary methodologies.
The creators
Mariia Tiurina (
Atul Chaturvedi (@Atulc), CyberSecurity Architect at Fiskars Group, Finland
Vasilis Skourtis (@vasilis.skourtis), Software Engineer at Intralot, Greece
Emette Cohen Douglen (@Cupid)
Michal Kamensky (@michal), Security Researcher, Bounce Security, Israel
Threat model
Summary
Which threat modeling framework(s) used and why
We used STRIDE threat model framework for security (the template we used, created by
Diagramming or thinking tool(s) used and why
We used draw.io for diagramming since it is a well-known free-to-use tool and easy to work in layers by each individual when they have time.
What is the scope of the threat model?
The scope of the threat model was a microservice application(RideShare) and associated directly interacting entities such as data stores, middleware, and 3rd party entities.
RideShare is an app that connects passengers and drivers for rides. The RideShare consists of a passenger app, a driver app, a dispatched optimization system (DISCO), and a backend server database.
- The passenger app
- The driver's app
The driver is also provided with the following services from the app- instant cashout to the bank, tracking earnings, getting updates of high demand areas, 24/7 customer support and safety toolkit, finance planner, registration including license validation, analytics logging.
- DISCO uses mobile phones to match the drivers with riders.
- The server side provides all of these features by adding new areas, coverage tracing, access point accuracy, calculating ETAs and finding the shortest route, tracking location, and finding the driver closest to the available or, soon to be free, driver.
What are the top threats you identified? What are the mitigation plans?
- Driver could be spoofed
- Employees' accounts can be compromised and used by attackers due to the lack of proper security training. E.g., an attacker can use
- a 2FA fatigue attack to hijack an employee's account
- phishing and spear phishing attacks
How did you prioritize the threats for mitigation?
We first threat based on the criticality factor of risk and the mitigations we could easily do within our control around the application environment.
How did you evaluate your threat model?
We think our model was quite descriptive, considering the breadth and depth of coverage possible within given timelines. However, It can be even better with further iterations.
Retrospective
If you were to give this threat model to the developer team, what do you think their reaction would be? How valuable do you think they’d find it?
We think the threat model could enlighten the development team and would be useful in developing test cases. However, development teams need to look at this threat model with the respective scope of development and how that scope could impact the surrounding scope of application.
About the creators
The creators of this threat model is champions of our Spring 2023 Hackathon.” Let’s hear about their hackathon story.
Who are on your team?
- Mariia Tiurina, Sr. Security Engineer at EPAM System, Israel (Captain)
- Atul Chaturvedi, CyberSecurity Architect at Fiskars Group, Finland
- Vasilis Skourtis, Software Engineer at Intralot, Greece
- Emette Cohen Douglen
- Michal Kamensky, Security Researcher, Bounce Security, Israel
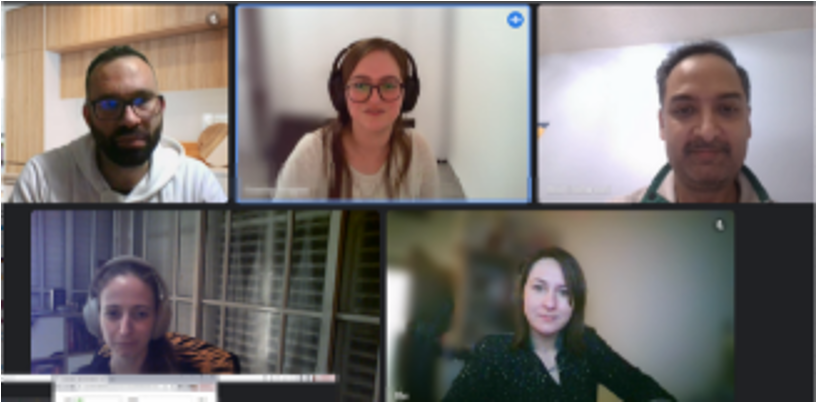
How did you work together?
We worked in an online meeting setup, planning a meetup before each milestone. However, depending on one's availability, we catch up almost daily to discuss the steps we were in at that moment. We also shared responsibilities, where we owned some areas and contributed. E.g. Atul created an initial diagram based on case studies while Mariia was developing an Excel format of steps to take.
What was the biggest challenge you faced? How did you overcome it?
The biggest challenge was the availability of team members since we all worked full-time in our primary jobs and were tired while connecting during late evening/night threat modeling sessions. To overcome this challenge, we kept the meetings casual, allowed ourselves to go off topics occasionally, and shared some funny moments of our days. Some of us were also contributing when we got some time during the day.
What are other activities you did that helped “Threat Modeling”?
After the first Checkpoint, we decided to dive into the “Threat Modeling” way of thinking. Best way to do it - play games!
We started from OWASP Cornucopia. After several rounds, we switched to Elevation of Privileges game by
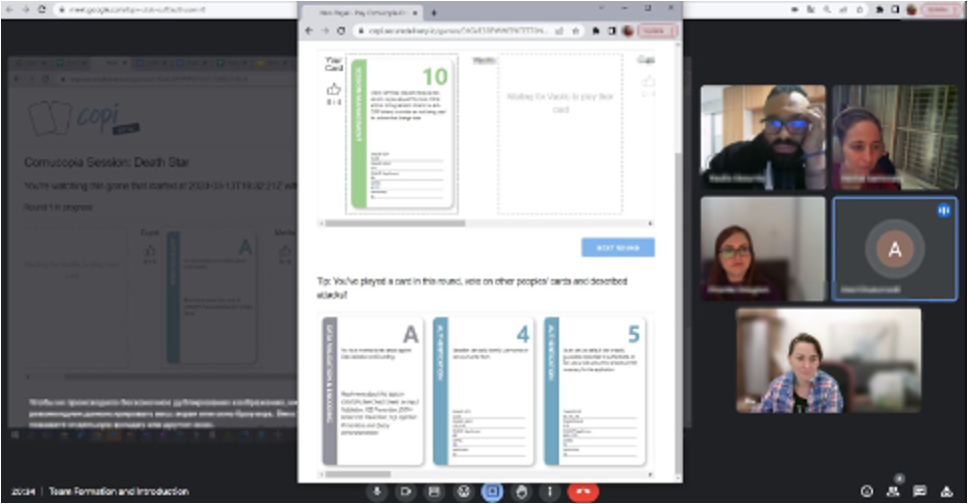
The EoP appeared to be more relevant to our task. We used DFD of our system and picked cards from the same category and applicable to the sameDFD element each round.
About Threat Model Collections
In this content series, we’ll publish and curate different threat model examples. The threat models can take many forms, such as graphical, textual representations or code. The models use diverse technologies, methodologies and techniques.



